Amanda Belichick stands as one of the most respected and influential figures in modern women’s collegiate lacrosse. Although her last name immediately draws attention due to her father, Bill Belichick—one of the most successful coaches in NFL history—Amanda has spent decades meticulously building her own identity, philosophy, and reputation in the world of sports. Her journey from student-athlete to one of the most recognizable lacrosse coaches in the country reflects discipline, persistence, and genuine passion for athlete development. This article aims to explore her life, upbringing, career progression, coaching values, leadership style, personal life, and the unique ways she has shaped the trajectory of women’s athletics.
Early Life and Influences
Growing Up in a Coaching Household
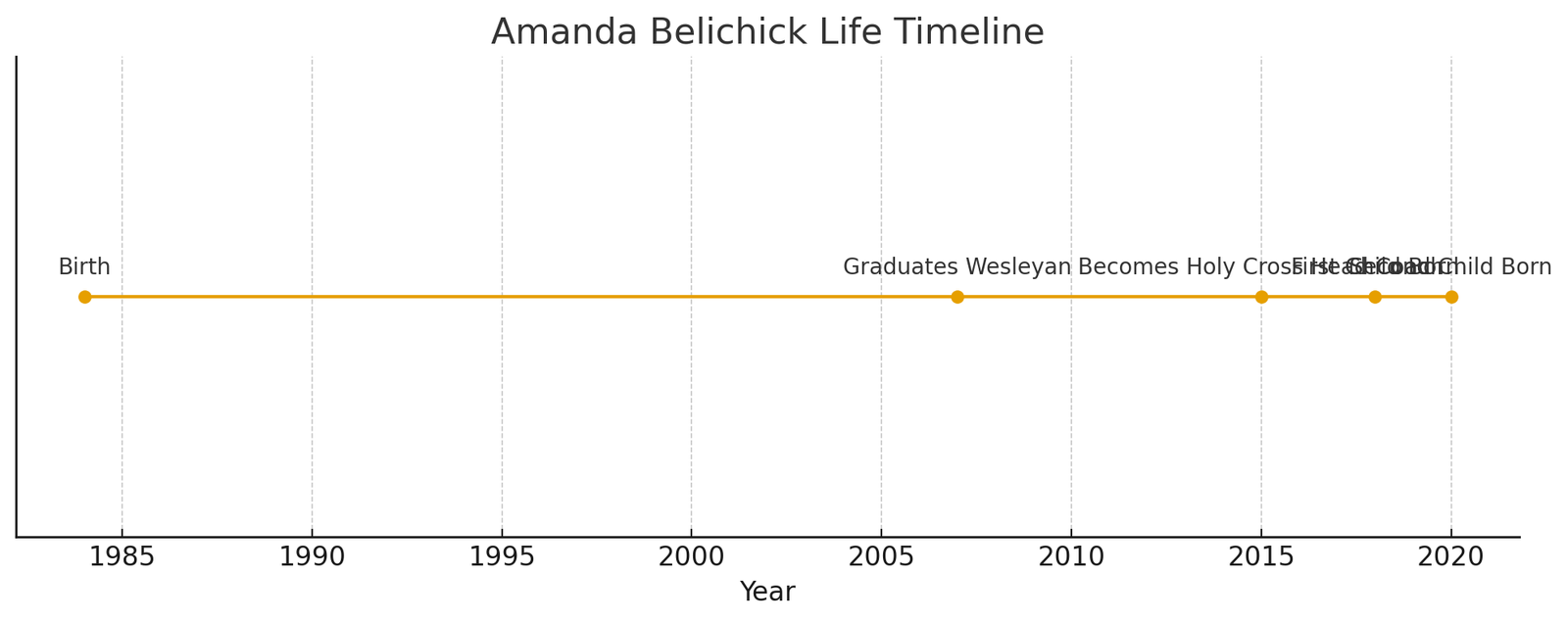
Born in 1984 in Weston, Massachusetts, Amanda Belichick spent her early years surrounded by the rhythms, rituals, and responsibilities of professional sports coaching. Her father, Bill Belichick, was deeply immersed in football strategy, analysis, and leadership, and although Amanda did not initially envision a future in coaching, she absorbed many of the values that define strong athletic mentorship: preparation, discipline, adaptability, and an empathetic but demanding leadership presence.
Her mother, Debby Clarke Belichick, also played a meaningful role in shaping Amanda’s balanced outlook on competitive sports and personal integrity. Alongside her two younger brothers—Steve and Brian, who would both follow coaching paths—Amanda’s childhood was infused with teamwork, communication, and constant exposure to the complexities of sports ecosystems.
Developing a Passion for Athletics
While her father’s world was football, Amanda found her love for lacrosse early. The sport’s intense pace, strategic nature, and physical rigor appealed to her athletic instincts. Throughout her youth she emerged as a committed, disciplined multi-sport athlete before eventually focusing primarily on lacrosse. Her early experiences as both a team leader and player laid the foundation for the leadership style she would later refine as a coach.
Education and Collegiate Athletic Career
Wesleyan University Years
Amanda attended Wesleyan University, a prestigious liberal arts college known not only for its academics but also for fostering strong athletic programs. She majored in history—a discipline that strengthened her analytical thinking, writing, and long-term strategic reasoning. Academically ambitious and athletically driven, she quickly became a standout member of the Wesleyan women’s lacrosse team.
Leadership on the Field
During her four years at Wesleyan, Amanda earned the status of a four-year letter winner and eventually served as senior captain. This role allowed her to experiment with leadership dynamics, balancing responsibility, mentorship, discipline, and collaboration. Teammates often described her as calm but assertive—someone who led through consistent effort rather than sheer volume.
Her experience as a student-athlete also strengthened her respect for academic balance and athlete well-being, themes she would later infuse into her coaching philosophy.
Early Career Path and Entrance into Coaching
A Non-Linear Journey into Athletic Leadership
After her graduation in 2007, Amanda did not immediately leap into coaching. Instead, she explored other professional opportunities—working briefly in advertising and other roles unrelated to athletics. These experiences helped refine her interpersonal communication skills and offered a broader understanding of professional environments outside the field.
However, lacrosse pulled her back, as she eventually took an opportunity to coach at Choate Rosemary Hall, a prestigious preparatory school in Connecticut. This became a turning point, awakening Amanda to a passion for mentorship, skill development, and helping young women find confidence in their athletic abilities.
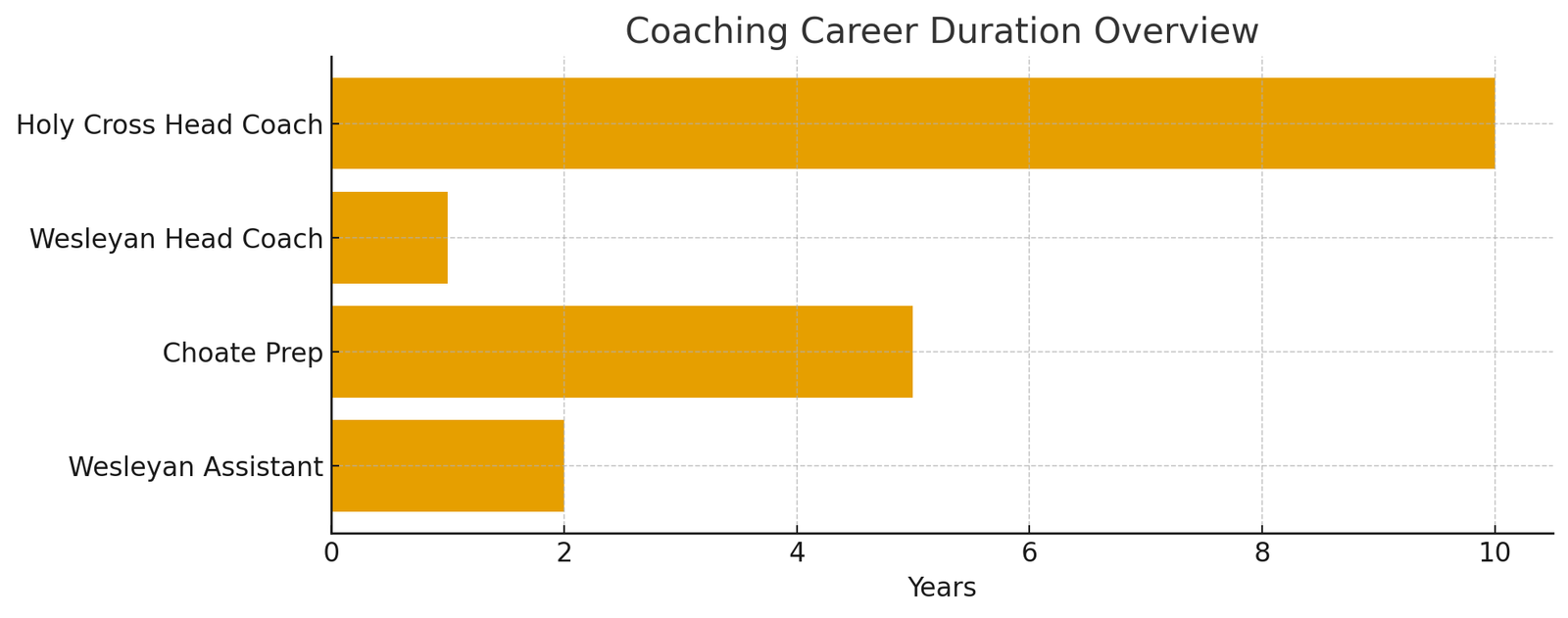
Assistant Coaching Roles and Skill Building
Amanda’s early coaching career included roles as an assistant coach at universities such as UMass and Ohio State. These positions allowed her to apprentice under seasoned coaches, observe a variety of systems, and recognize the importance of adapting coaching methods to different team cultures.
Her responsibilities included:
- Recruiting new talent
- Designing practice plans
- Mentoring athletes academically and athletically
- Assisting with strategic development during competition
These formative years were vital in shaping her holistic approach—a blend of discipline, collaboration, and individualized athlete support.
Rise to Head Coach: Wesleyan and Holy Cross
Return to Wesleyan as Head Coach
In 2014, Amanda returned to her alma mater as head coach, marking her first major leadership role. Although her time as head coach at Wesleyan was brief, it was impactful. She reenergized the program, improved team morale, and deepened the mentorship culture around the players.
Holy Cross: A Defining Era
In 2015, Amanda Belichick accepted the position of head coach for the women’s lacrosse team at the College of the Holy Cross. This role became the cornerstone of her coaching legacy.
Building a Culture of Trust and Growth
At Holy Cross, Amanda emphasized:
- Accountability
- Confidence building
- Personal development
- Cohesiveness and unity
- Mental strength and resilience
Her leadership style is grounded in authentic connection. She often states that coaching is not just about athletic performance but helping players develop into well-rounded individuals capable of meeting life’s challenges with poise and confidence.
Long-Term Program Development
Over the years, Amanda improved recruitment, strengthened training regimens, modernized tactical strategies, and fostered a positive emotional environment for athletes. Her consistent presence and long-term planning have made her one of the most respected coaches in collegiate lacrosse.
Coaching Philosophy and Leadership Approach
A Holistic View of Athlete Development
Amanda Belichick’s coaching philosophy integrates mental, physical, emotional, and academic well-being. She prioritizes:
- Open communication
- Emotional safety within the team
- Developing internal motivation
- Encouraging leadership among players
- Fostering independence and self-awareness
She believes that athletes perform best when they feel supported as humans, not merely as performers.
Strategic Flexibility and Player-Centered Tactics
Tactically, Amanda values adaptability. She does not force a rigid playing style; instead, she evaluates the strengths of each roster and shapes strategies around them. This flexibility marks her as a modern coach who prioritizes creativity and collaboration.
Lessons from Her Father, Bill Belichick
While Amanda did not intentionally pursue her father’s career path, she acknowledges that she learned several lessons from him:
- Preparation is non-negotiable
- Small details determine outcomes
- Teamwork supersedes individual fame
- Consistency is essential to long-term success
Yet she diverges in key ways, especially in communication style—adopting a more relational and emotionally supportive approach suited to her athletes.
Personal Life
Outside the field, Amanda maintains a grounded and balanced personal life. She married AJ DeSantis, and the couple now have two children. Her identity as a mother deeply influences her compassion, patience, and understanding of the pressures young women face in collegiate athletics.
She also values privacy, choosing to share only select aspects of her life publicly. This balance between visibility and privacy showcases professionalism and integrity.
Public Perception and Legacy
Making Her Own Name in the Sports World
Although many initially identify Amanda as “Bill Belichick’s daughter,” her career success demonstrates her independence and competence. Over time, her name has become a respected brand within women’s athletics, and her players consistently praise her mentorship, communication, and authenticity.
A Role Model for Women in Coaching
Amanda represents the growing movement of women breaking barriers in coaching—especially in sports traditionally dominated by male leadership structures. Her journey highlights vital truths:
- Coaching excellence is not gender-bound
- Leadership can be empathetic and firm simultaneously
- Women can command powerful influence in collegiate athletics
Her example inspires young athletes and aspiring coaches, particularly women seeking long-term careers in sports.
Frequently Asked Questions
Who is Amanda Belichick?
Amanda Belichick is an American lacrosse coach and the head coach of the women’s lacrosse team at the College of the Holy Cross. She is the daughter of NFL coach Bill Belichick but has forged a highly respected career of her own in collegiate athletics.
What is Amanda Belichick’s coaching style?
Her coaching style is holistic, supportive, and athlete-centered. She focuses on developing players as individuals—emotionally, mentally, and academically—while also implementing adaptable tactical systems.
Did Amanda Belichick play lacrosse?
Yes. She played lacrosse at Wesleyan University, where she was a standout athlete and served as team captain during her senior year.
How long has she coached at Holy Cross?
Amanda began coaching at Holy Cross in 2015 and has since become one of the longest-tenured lacrosse coaches at the institution.
Is Amanda Belichick married?
Yes. She is married to AJ DeSantis, and they have two children together.